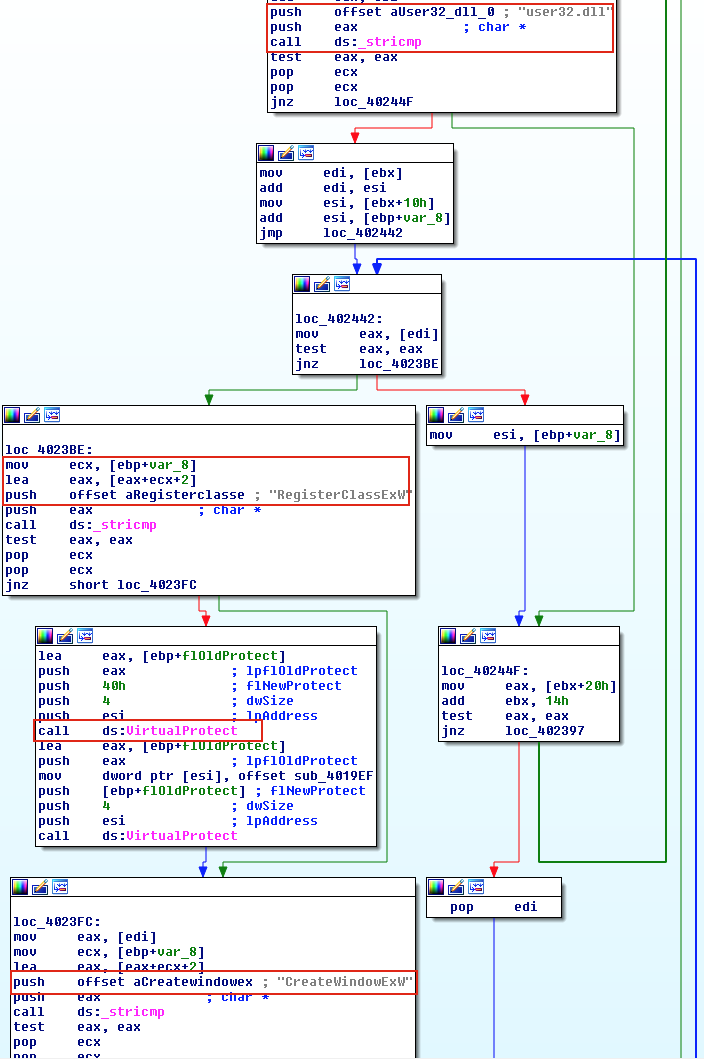
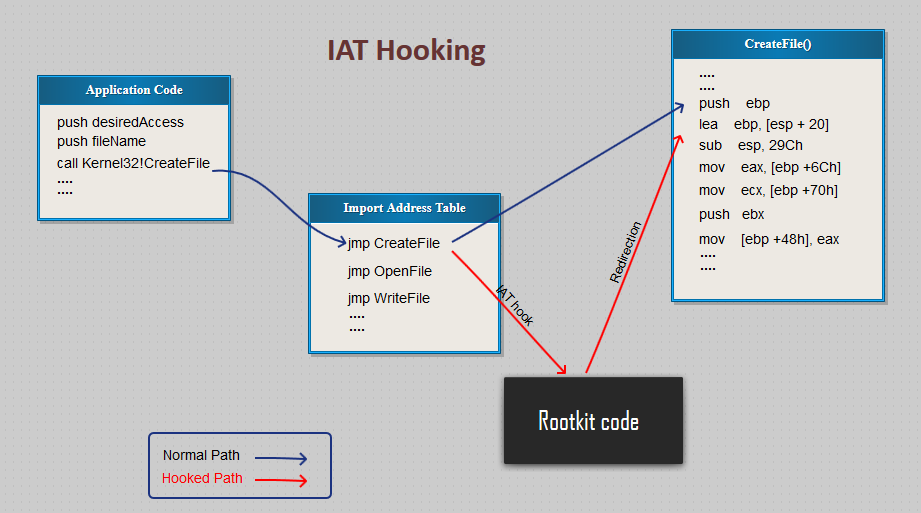
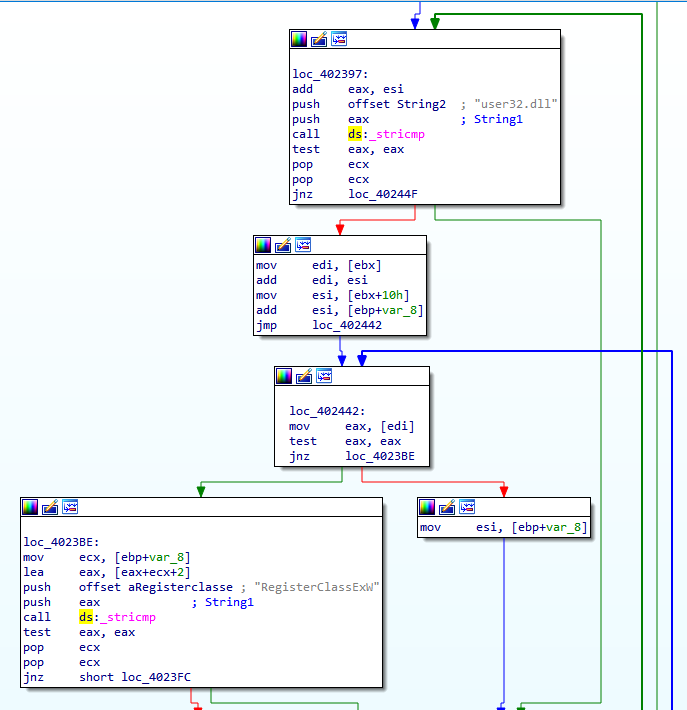
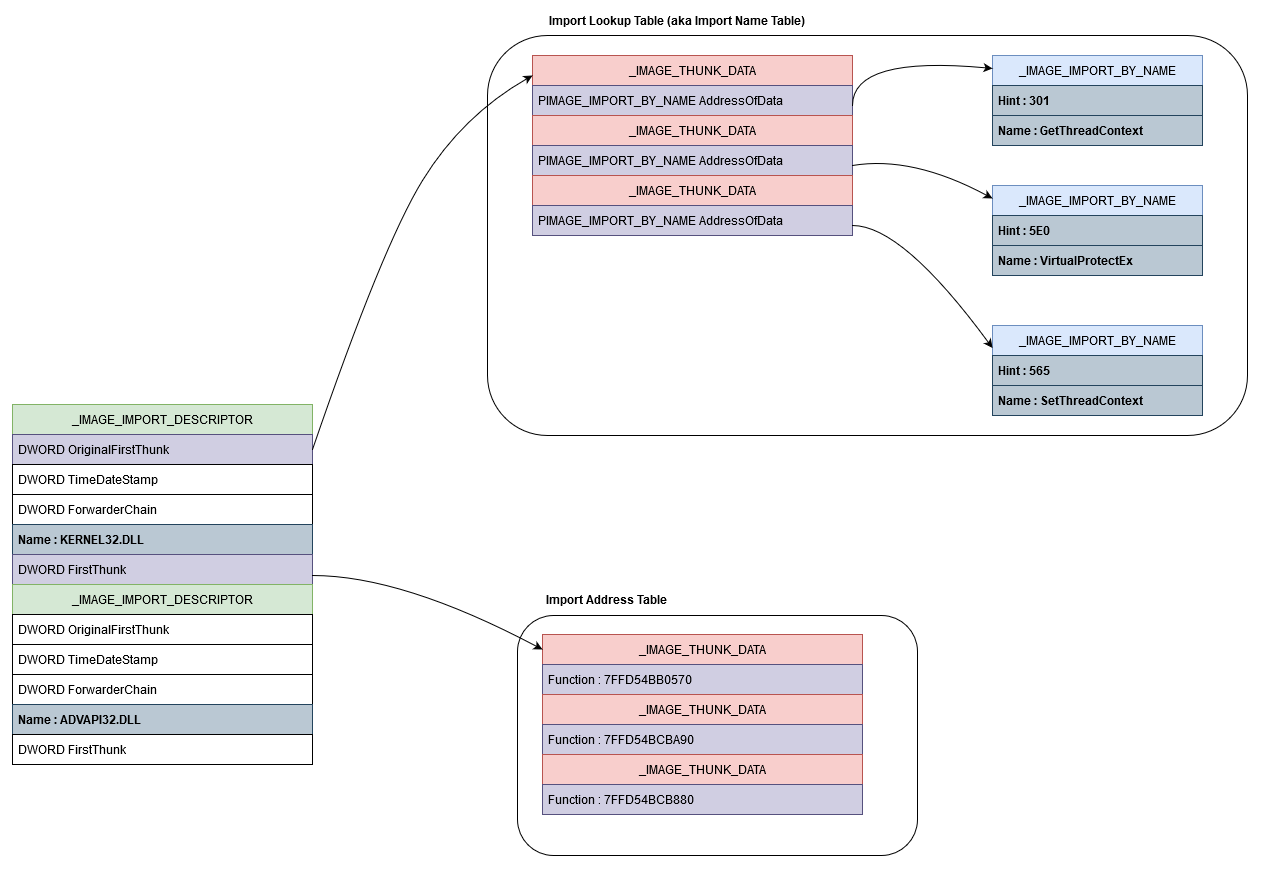
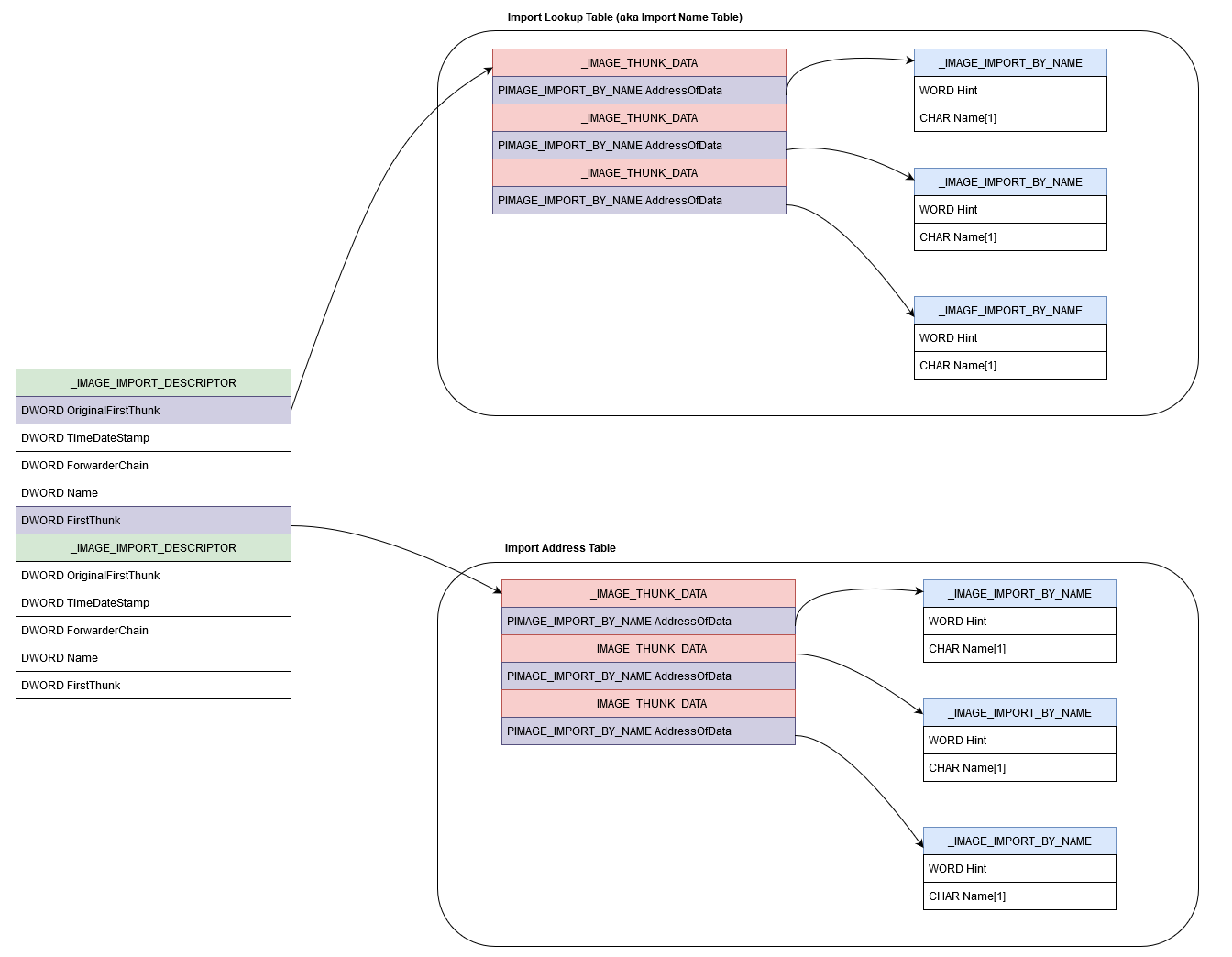
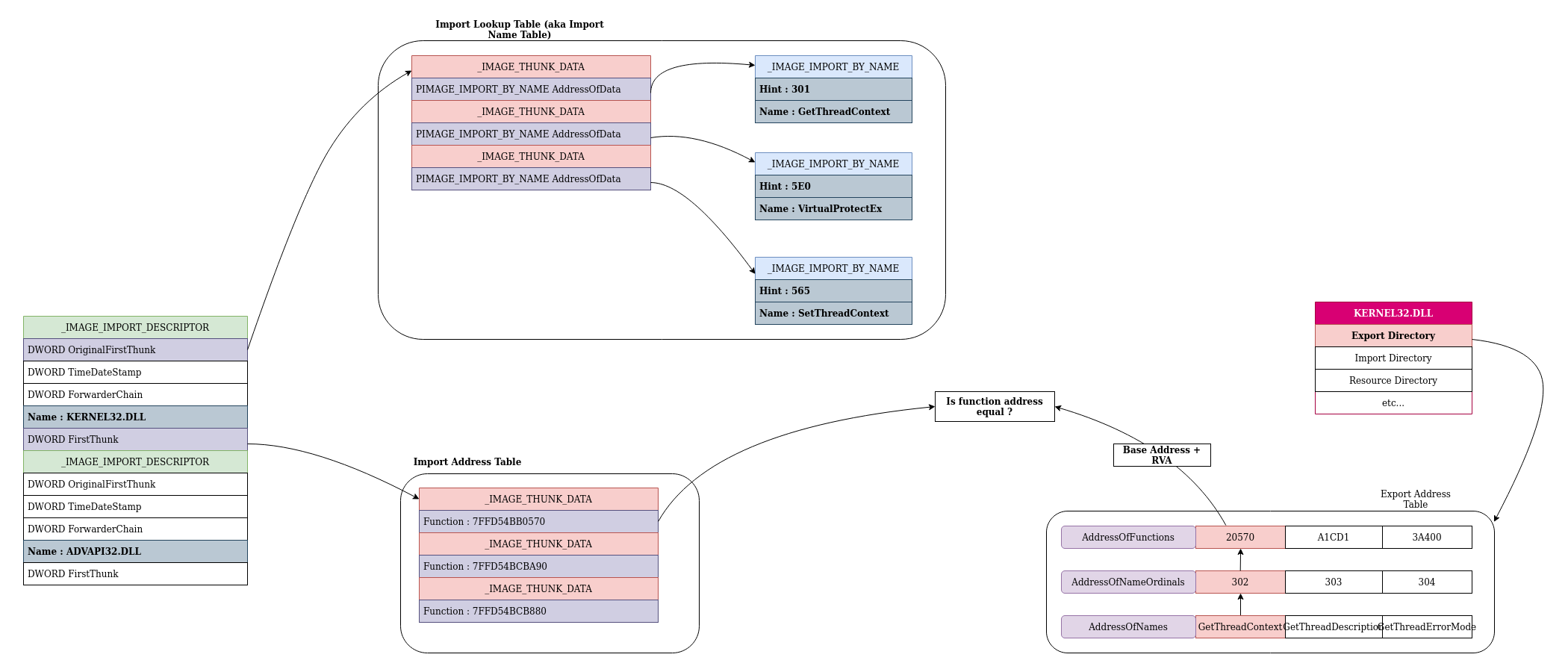
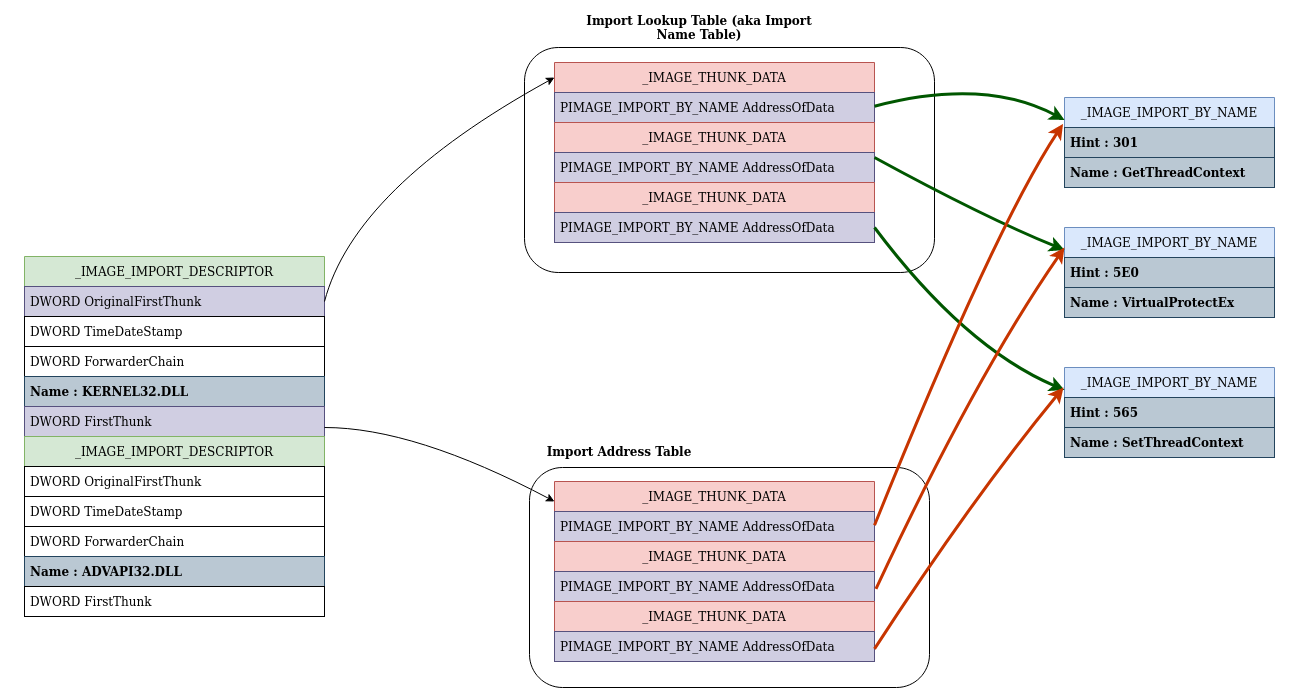
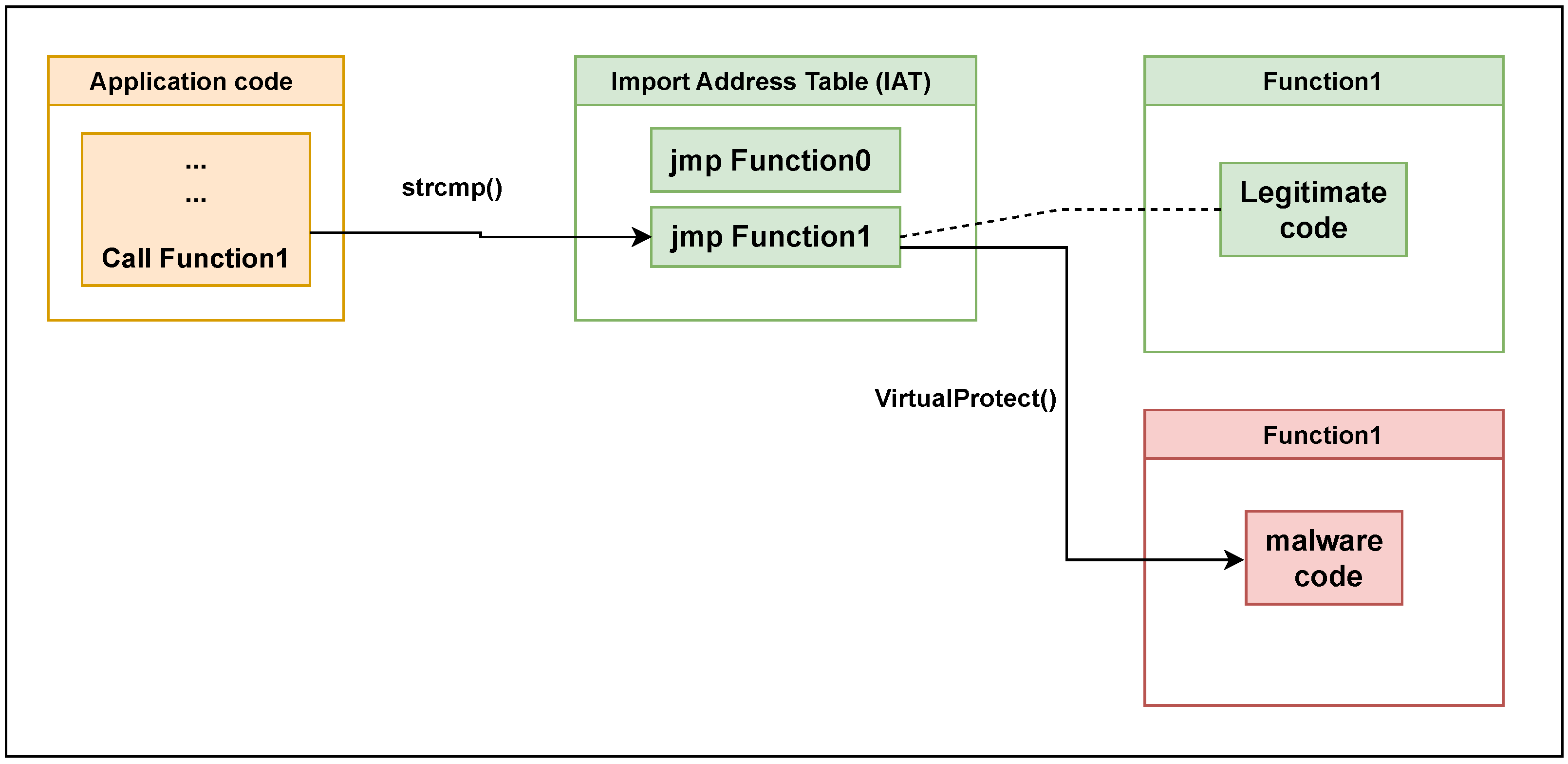
GitHub - m0n0ph1/IAT-Hooking-Revisited: Import address table (IAT) hooking is a well documented technique for intercepting calls to imported functions.
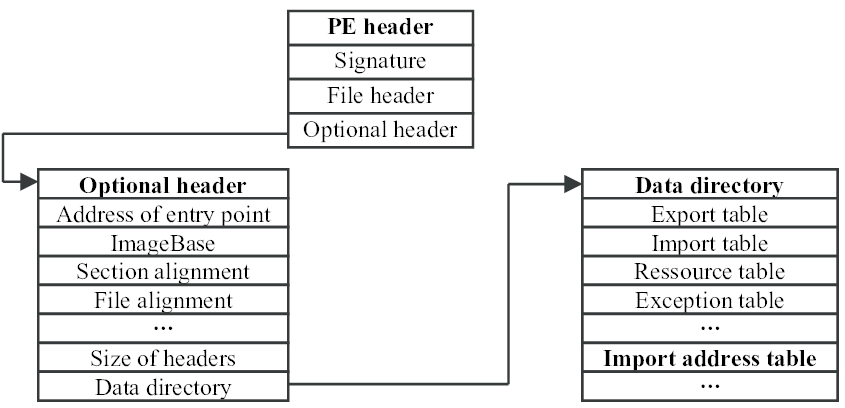
Applied Sciences | Free Full-Text | Malware API Calls Detection Using Hybrid Logistic Regression and RNN Model

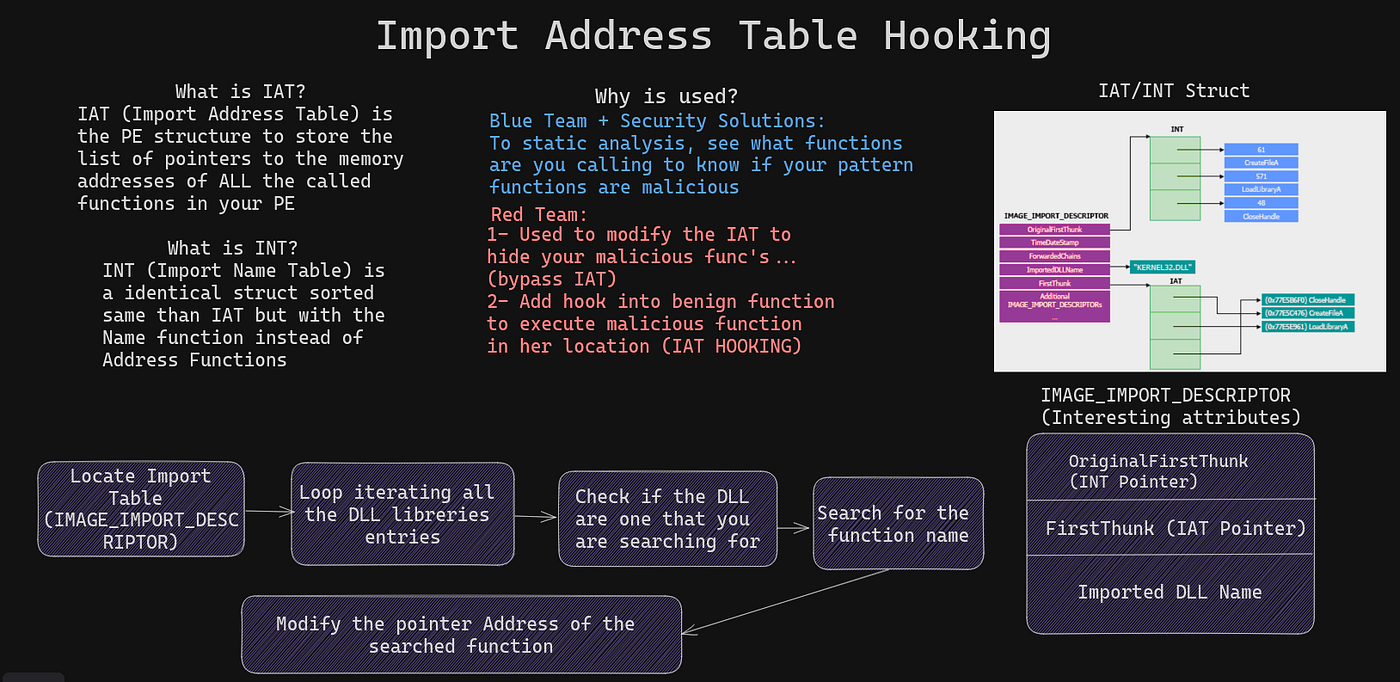
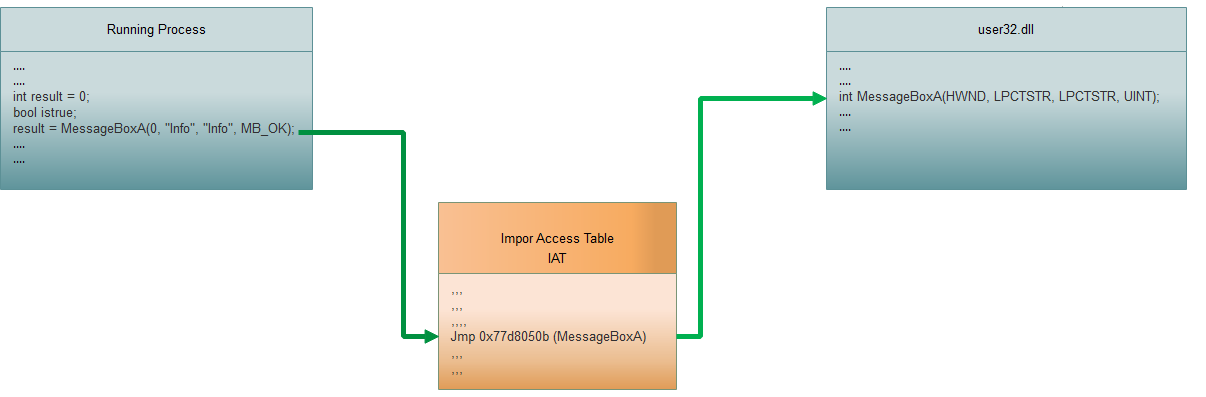
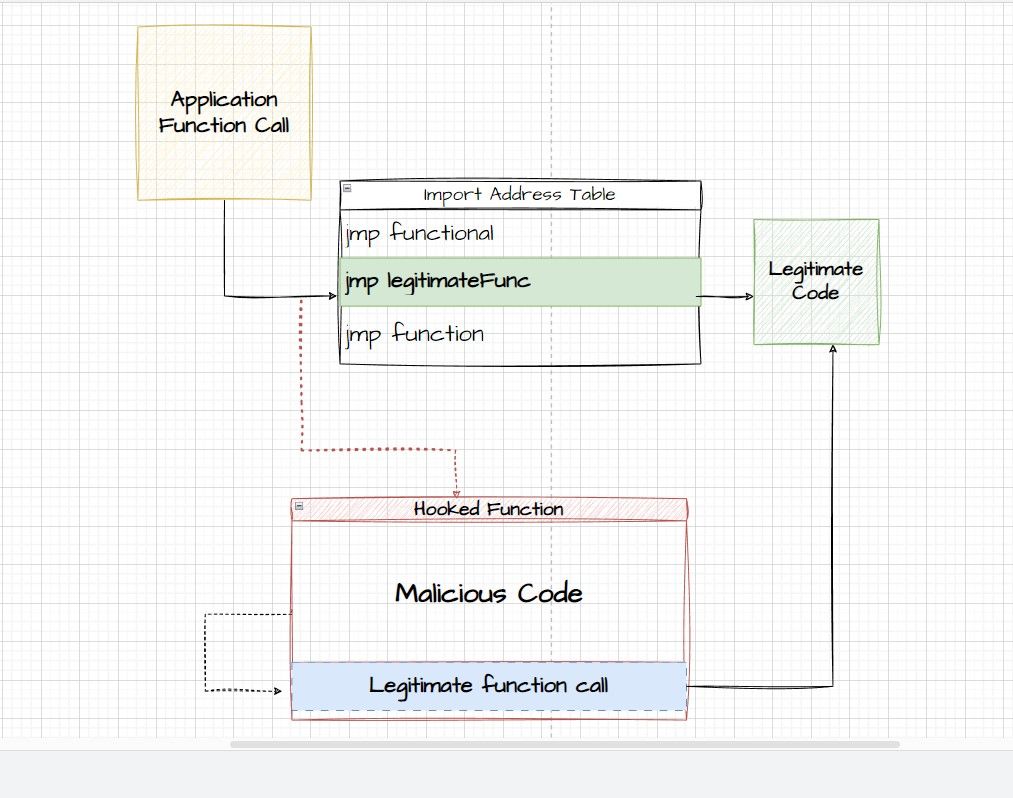
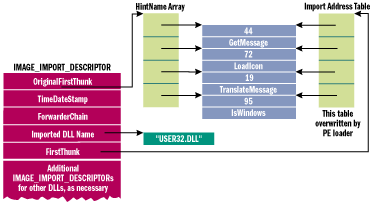
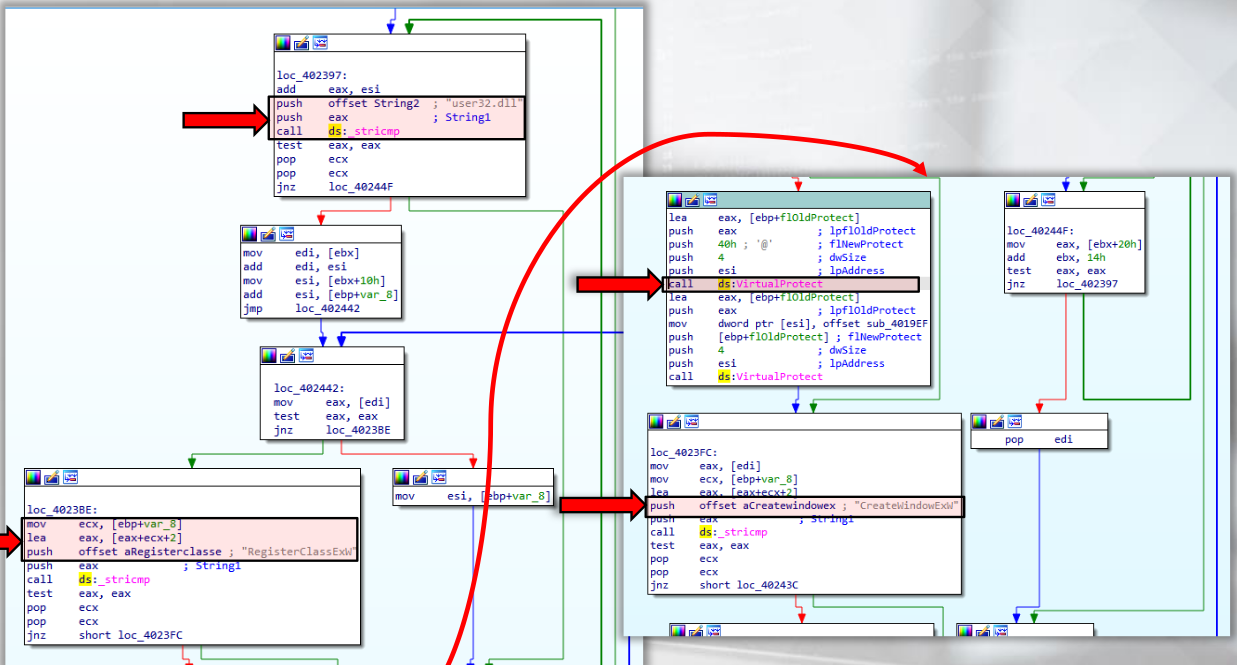
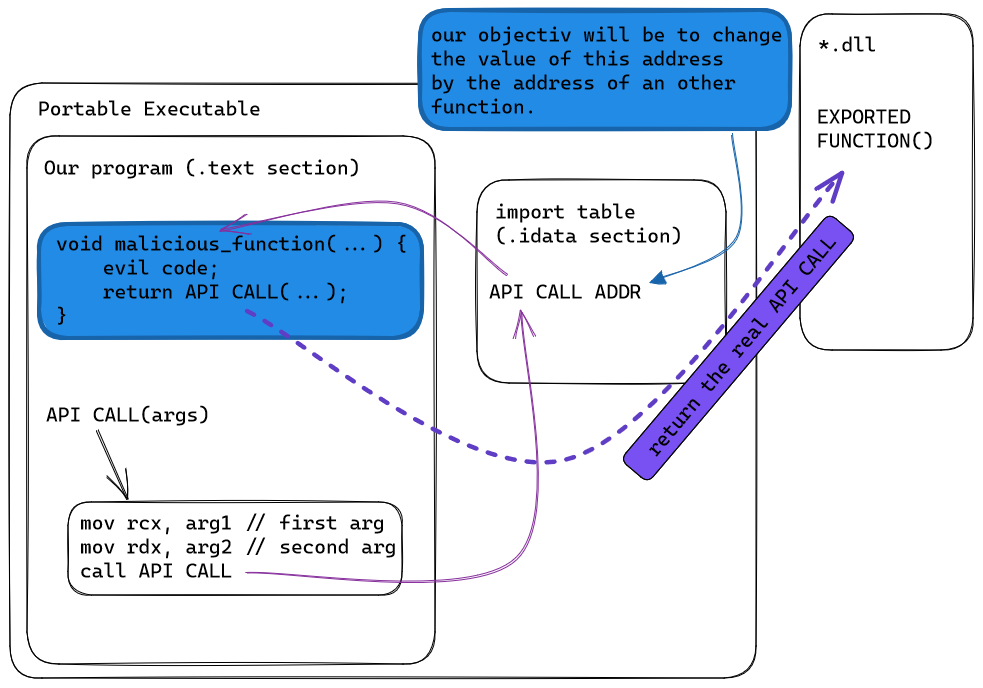
Clint Gibler on X: "🥇 Best EDR Of The Market An AV/EDR Bypassing Lab for Training & Leaning Purposes Understand & bypass detection mechanisms employed by many well-known EDRs → IAT hooking,